Designing Azure Cloud Solutions with Security Best Practices Part 2
- Feb 22
- 2 min read

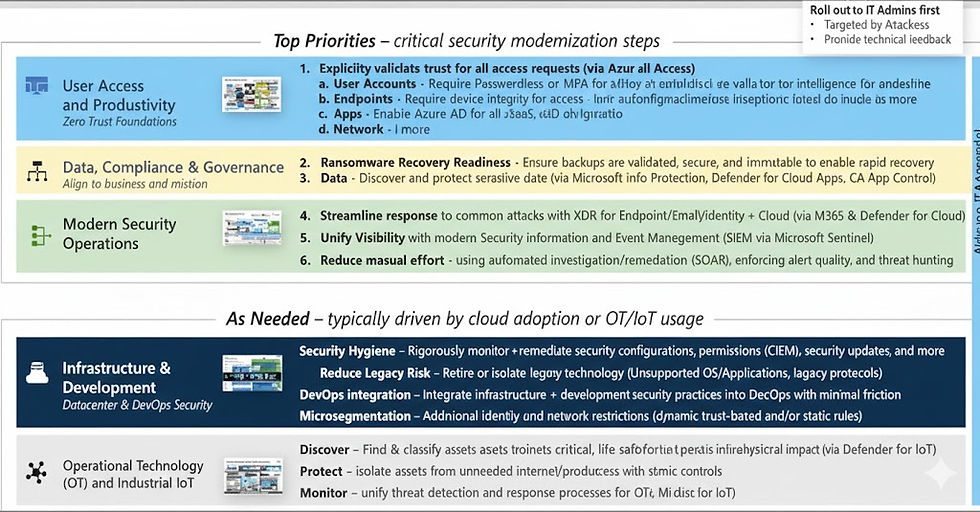
Zero Trust Initiatives
Zero Trust is a major security transformation, not a single product or feature.
Organizations must prioritize initiatives that deliver the highest security impact with the lowest effort.
The goal is to reduce risk quickly without requiring massive time, budget, or staffing.
Microsoft’s Zero Trust Rapid Modernization Plan (RaMP) provides a proven prioritization framework.
RaMP is part of the Microsoft Cybersecurity Reference Architecture (MCRA).
It identifies high‑value, low‑effort controls that stop the most common modern attacks.
RaMP focuses on identity, endpoints, apps, data, network, and infrastructure modernization.
It accelerates adoption of MFA, Conditional Access, device compliance, segmentation, and app governance.
RaMP improves both security posture and user productivity at the same time.
It enables organizations to modernize fast, show measurable progress, and build momentum for full Zero Trust adoption.
Six Fundamental Elements

Top Priorities
Identity Zero Trust Deployment Objectives
Cloud identity is federated with on‑premises identity systems to unify authentication.
Conditional Access policies control access and enforce remediation when risk is detected.
Identity analytics increase visibility into authentication patterns and anomalies.
Identity governance manages lifecycle, access privileges, and entitlement workflows.
User, device, location, and behavior signals are evaluated in real time to determine risk.
Threat signals from other security tools are integrated to strengthen detection and response.
Application Zero Trust Deployment Objectives
Gain visibility into application activity and data by connecting apps through APIs.
Discover and control the use of shadow IT across the environment.
Automatically protect sensitive information and high‑risk activities using policies.
Deploy adaptive access and session controls for all applications.
Strengthen defenses against cyber threats and untrusted or rogue applications.
Assess and improve the security posture of cloud application environments.
Endpoint Zero Trust Deployment Objectives
Register all endpoints with a cloud identity provider to gain full visibility across user devices.
Ensure access is granted only to cloud‑managed and compliant devices and applications.
Enforce data loss prevention (DLP) policies across corporate and BYOD devices.
Monitor device risk using endpoint threat detection and centralized management.
Route endpoint logs and events to a SIEM for actionable insights and alerts.
Apply access controls based on real‑time endpoint risk for both corporate and BYOD devices.
Integrate endpoint risk signals from Defender for Endpoint or MTD solutions into Conditional Access.
Conclusion
Together, the Identity, Application, and Endpoint deployment objectives form a unified foundation for accelerating Zero Trust maturity. By strengthening identity as the primary control plane, securing applications through visibility and adaptive governance, and enforcing device health and risk‑based access across all endpoints, organizations create a resilient, intelligence‑driven security posture. These initiatives work in concert to reduce attack surface, eliminate implicit trust, and ensure that every access request is continuously validated based on real‑time risk. Implemented collectively, they deliver measurable improvements in protection, operational efficiency, and user experience—establishing a scalable path toward full Zero Trust adoption.


Comments